Data Security and Privacy
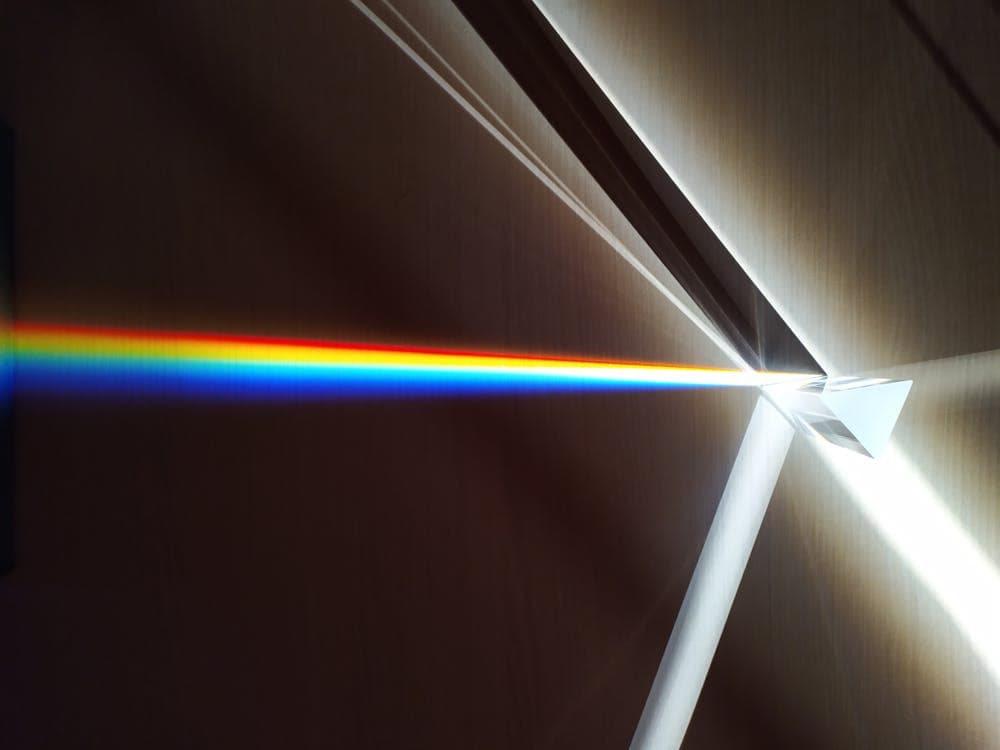
IntermediateData security and privacy encompass the principles, technologies, and practices used to protect digital information from unauthorized access, corruption, theft, and misuse throughout its entire lifecycle. At the core of data security lies cryptography: symmetric encryption algorithms like AES protect data with a single shared key for speed and efficiency, while asymmetric encryption using public-private key pairs (RSA, ECC) enables secure key exchange and digital signatures without requiring a pre-shared secret. Hashing algorithms such as SHA-256 produce fixed-length fingerprints of data, enabling integrity verification and secure password storage. Together, these cryptographic primitives form the foundation for securing data at rest, in transit, and in use.
Data privacy extends beyond technical protections to address how personal information is collected, processed, stored, and shared. Regulatory frameworks such as the General Data Protection Regulation (GDPR) in Europe, the California Consumer Privacy Act (CCPA) in the United States, and sector-specific laws like HIPAA for healthcare impose legal requirements on organizations handling personal data. Key concepts include data classification (categorizing data by sensitivity level), Personally Identifiable Information (PII) protection, data minimization (collecting only what is necessary), purpose limitation, and individual rights such as access, rectification, and erasure. Organizations must implement both technical controls and governance policies to achieve compliance.
Modern data security also addresses the challenges of cloud storage, big data analytics, and emerging technologies. Secure data storage requires encryption at rest, access controls, key management systems, and secure deletion procedures. Data lifecycle management governs information from creation through storage, use, sharing, archival, and destruction. Privacy-enhancing technologies such as differential privacy, homomorphic encryption, and data anonymization techniques enable organizations to derive insights from sensitive data while minimizing privacy risks. As data volumes grow exponentially and regulatory landscapes evolve, the intersection of security and privacy has become one of the most critical domains in cybersecurity.
Practice a little. See where you stand.
Quiz
Reveal what you know — and what needs work
Adaptive Learn
Responds to how you reason, with real-time hints
Flashcards
Build recall through spaced, active review
Cheat Sheet
The essentials at a glance — exam-ready
Glossary
Master the vocabulary that unlocks understanding
Learning Roadmap
A structured path from foundations to mastery
Book
Deep-dive guide with worked examples
Role-play
Think like an expert — no grading
Key Concepts
One concept at a time.
Explore your way
Choose a different way to engage with this topic — no grading, just richer thinking.
Explore your way — choose one:
Curriculum alignment— Standards-aligned
Grade level
Learning objectives
- •Compare symmetric and asymmetric encryption and explain when to use each in real-world scenarios
- •Describe how hashing and salting work together to protect stored passwords from rainbow table and brute-force attacks
- •Apply data classification frameworks to categorize information by sensitivity and assign appropriate security controls
- •Explain the core principles of GDPR including data minimization, purpose limitation, and breach notification requirements
- •Analyze the differences between data anonymization and pseudonymization and their implications under privacy regulations
- •Design a key management strategy using envelope encryption, HSMs, and key rotation policies
- •Evaluate secure data destruction methods and explain why standard deletion and formatting are insufficient
- •Describe how differential privacy enables data analysis while providing mathematical privacy guarantees